As we look ahead to 2026, the world of cybersecurity is poised to undergo profound changes. With rapid advancements in technology, the digital landscape will continue to evolve, presenting both new challenges and innovative solutions. The rise of AI, IoT, 5G, and other emerging technologies will introduce novel threats, while cybersecurity professionals and organizations must adapt to mitigate the risks. This article explores the anticipated threats in the cybersecurity space by 2026, as well as the strategies and solutions that will shape the future of a safer digital world.
The Evolving Cyber Threat Landscape

1. AI-Powered Cyberattacks
One of the most significant changes we can expect in the cybersecurity threat landscape by 2026 is the rise of AI-powered cyberattacks. Artificial intelligence (AI) has already begun to shape many industries, from healthcare to finance, but cybercriminals will soon use AI to enhance their malicious capabilities.
AI’s ability to process vast amounts of data and learn patterns will allow hackers to automate and improve their attack strategies. One example is the potential rise of AI-driven phishing attacks, where cybercriminals use machine learning algorithms to craft hyper-targeted, highly convincing phishing emails. These emails may leverage data from social media profiles, previous communications, and other online footprints to seem more legitimate.
AI will also be used in automated vulnerability scanning, enabling hackers to quickly find and exploit weaknesses in systems. Unlike traditional attacks, these AI-driven threats will be faster, more intelligent, and able to evolve in response to defence mechanisms, making them harder to predict and prevent.
2. Quantum Computing and Encryption Vulnerabilities
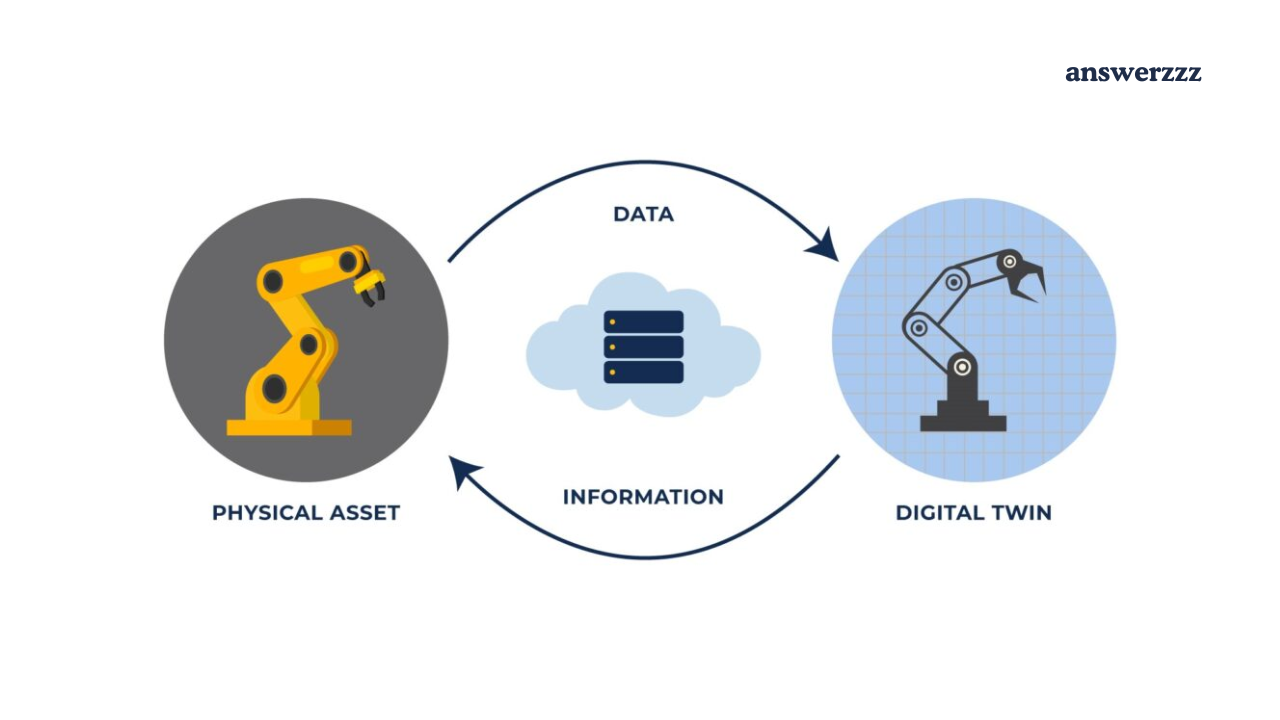
How AI-Driven Robotics Are Revolutionizing Manufacturing in 2026
Quantum computing, a field that is rapidly advancing, will have profound implications for cybersecurity. By 2026, it’s expected that quantum computers will be able to break many of the encryption algorithms that currently protect sensitive data. Quantum computers operate on principles of quantum mechanics, allowing them to perform certain calculations exponentially faster than classical computers. This ability could potentially render current cryptographic systems useless.
In particular, algorithms like RSA and Elliptic Curve Cryptography (ECC), which are commonly used to secure communications and sensitive data, could be easily cracked by quantum machines. This presents an existential threat to the security of digital communications, banking systems, and online transactions.
Organizations will need to adopt post-quantum cryptography (PQC) solutions to protect their data from quantum threats. PQC algorithms are designed to be resistant to quantum computer attacks and will become crucial for ensuring the future of data protection in a quantum computing era.
3. Cyberattacks on IoT Devices
The Internet of Things (IoT) has already created a vast network of connected devices, and by 2026, it is expected that there will be billions of such devices in use. These devices, ranging from smart home appliances to industrial sensors, often lack robust security features, making them attractive targets for cybercriminals.
IoT botnets, like the infamous Mirai Botnet, which was used in large-scale DDoS attacks, will likely evolve to be more sophisticated and harder to defend against. IoT devices, particularly those with weak or default passwords, could be hijacked and used to launch devastating attacks on critical infrastructure, including power grids, healthcare systems, and manufacturing plants.
To counteract these threats, manufacturers will need to prioritize IoT security by design, ensuring that devices are equipped with strong encryption, secure boot processes, and regular firmware updates. Consumers will also need to take responsibility by changing default passwords, disabling unused features, and investing in IoT security solutions.
4. Deepfakes and Misinformation

By 2026, the use of deepfake technology will likely be widespread, making it easier to create convincing audio and video content that is entirely fabricated. These technologies could be used maliciously to spread misinformation, manipulate public opinion, or impersonate individuals for fraudulent purposes.
Deepfakes present a unique challenge for cybersecurity, as they can be used to compromise reputations, influence elections, or defraud individuals. The ability to create hyper-realistic fake videos and audio could undermine trust in online content and complicate the detection of fraud.
Combating deepfakes will require advanced detection techniques, including the use of AI to spot inconsistencies in video or audio data. Furthermore, digital authentication technologies such as blockchain could play a critical role in ensuring the authenticity of online content by providing a verifiable trail for media assets.
Solutions and Strategies for a Safer Digital World in 2026
While the future of cybersecurity will undoubtedly present challenges, several innovations and solutions are emerging to counter these threats and build a safer digital world. Let’s explore some of the most promising strategies and technologies.
1. Artificial Intelligence for Defense
Just as cybercriminals are leveraging AI for malicious purposes, cybersecurity professionals are harnessing the power of AI to defend against threats. AI-powered threat detection systems will be crucial in identifying and neutralizing attacks in real time. By analyzing vast amounts of data and detecting patterns, AI can help identify unusual activity that may indicate a cyberattack, such as malware infections, phishing attempts, or network intrusions.
AI will also improve the speed and accuracy of incident response. Instead of waiting for a human analyst to detect and respond to an attack, AI-driven systems will be able to automatically take action to contain the threat, such as blocking malicious IP addresses, isolating infected systems, or alerting security teams. This will significantly reduce the time it takes to mitigate an attack and minimize potential damage.
2. Post-Quantum Cryptography
As quantum computers threaten to break traditional encryption systems, the adoption of post-quantum cryptography (PQC) will become essential. PQC algorithms are designed to withstand the processing power of quantum computers, ensuring that sensitive data remains secure even in the quantum era.
Leading organizations, such as the National Institute of Standards and Technology (NIST), are already working on standardizing PQC algorithms, and by 2026, we can expect the widespread adoption of these new cryptographic techniques. This will ensure that communications, transactions, and data storage remain secure in the face of quantum computing advancements.
In addition to PQC, organizations will likely embrace quantum key distribution (QKD), a method that uses the principles of quantum mechanics to enable the secure exchange of cryptographic keys. With the integration of these advanced cryptographic solutions, we can mitigate the risks posed by quantum computing.
3. Zero-Trust Security Model
As cyber threats grow more sophisticated, organizations will increasingly adopt the zero-trust security model. This approach assumes that no one, whether inside or outside the network, can be trusted by default. Every user, device, and network request must be verified before access is granted.
Zero trust relies on continuous authentication, multi-factor authentication (MFA), and strict access control policies to ensure that only authorized users and devices can access sensitive data. By implementing a zero-trust framework, organizations can limit the potential impact of insider threats and external attacks, making it much harder for cybercriminals to breach systems.
4. Blockchain for Data Integrity
Blockchain technology, known for its decentralized and tamper-resistant nature, has the potential to revolutionize cybersecurity in the coming years. By 2026, blockchain could be widely used to ensure the integrity of digital transactions, media, and other sensitive data.
In the context of cybersecurity, blockchain can be used to verify the authenticity of digital identities, secure transactions, and prevent data tampering. Its immutable ledger system ensures that once data is recorded, it cannot be altered or deleted without detection. This will help address issues such as deepfakes, data manipulation, and fraud, enhancing trust in digital communications.
5. Enhanced IoT Security
The proliferation of IoT devices will require stronger security measures to prevent attacks. By 2026, IoT manufacturers will likely implement more advanced security features as standard, including hardware-based security modules, encrypted communications, and secure boot processes.
Additionally, organizations will implement network segmentation to isolate IoT devices from critical systems and sensitive data. This will limit the impact of an attack on the IoT network and prevent it from spreading to other parts of the network. Regular software updates and patch management will also play a critical role in ensuring IoT devices remain secure over time.
6. Advanced Cybersecurity Training and Awareness

As cyber threats become more sophisticated, organizations must invest in ongoing cybersecurity training and awareness programs for employees. By 2026, we can expect these programs to evolve, incorporating immersive learning experiences using virtual reality (VR) or simulations to train employees on how to recognize and respond to cyber threats.
Additionally, companies will likely adopt behavioural analytics to detect risky user behaviour and provide targeted training to reduce human errors that could lead to cyber breaches. By building a culture of cybersecurity awareness, organizations can better equip their workforce to defend against social engineering attacks, such as phishing, and reduce the risk of insider threats.
The cybersecurity landscape in 2026 will be shaped by a combination of evolving threats and innovative solutions. As AI, quantum computing, and IoT technologies continue to develop, they will create new challenges for cybersecurity professionals. However, with the adoption of advanced technologies such as AI-powered defence systems, post-quantum cryptography, blockchain, and zero-trust security models, we can build a safer digital world.
Nanotechnology in Medicine: The Latest Innovations You Should Know
The key to a secure future lies in proactive measures: organizations must stay ahead of emerging threats by embracing cutting-edge technologies, adopting a zero-trust mentality, and continuously training their workforce. By doing so, we can ensure that the digital world remains a safe place for communication, commerce, and innovation well into the future.