Quantum cryptography represents a revolutionary approach to secure communication, leveraging the principles of quantum mechanics to enhance the confidentiality and integrity of information. As the digital landscape evolves, the necessity for robust security measures has never been more pressing. This article explores the foundational principles of quantum cryptography, its implications for the future of secure communication, and the challenges that lie ahead.
What is Quantum Cryptography?
Quantum cryptography is a method of securing communication that utilizes the principles of quantum mechanics, particularly the behaviour of quantum bits (qubits). Unlike classical bits, which can exist as either 0 or 1, qubits can exist in a state of superposition, allowing them to represent multiple values simultaneously. This unique property enables quantum cryptography to offer levels of security unattainable by classical cryptographic methods.
The most well-known application of quantum cryptography is Quantum Key Distribution (QKD), which allows two parties to generate and share a secret key over a potentially insecure channel. QKD ensures that any eavesdropping attempts can be detected, providing a strong foundation for secure communication.
The Basics of Quantum Mechanics
To understand quantum cryptography, it’s essential to grasp some fundamental principles of quantum mechanics:
1. Superposition
In classical computing, bits are the basic units of information and can exist in one of two states: 0 or 1. However, in quantum mechanics, qubits can exist in a superposition of states, which means they can represent both 0 and 1 simultaneously. This property allows quantum systems to process vast amounts of information more efficiently than classical systems.
2. Entanglement
Entanglement is a phenomenon where two or more qubits become correlated in such a way that the state of one qubit is dependent on the state of another, regardless of the distance separating them. When qubits are entangled, measuring the state of one qubit instantly influences the state of the other. This property is crucial for ensuring secure communication, as it allows parties to share a key that is inherently linked to the quantum states involved.
3. Quantum Measurement
When a measurement is made on a quantum state, it collapses the superposition into one of its possible states. This collapse is probabilistic and can change the state of the system. In the context of quantum cryptography, this means that if an eavesdropper attempts to intercept the communication, the act of measurement will alter the quantum states, alerting the legitimate parties to the presence of an intruder.
How Quantum Key Distribution Works
The Benefits and Challenges of Integrating AI into Everyday Life
Quantum Key Distribution (QKD) is the most significant application of quantum cryptography. It enables two parties, often referred to as Alice and Bob, to establish a shared secret key with unconditional security. The process typically follows these steps:
1. Preparation of Quantum States
Alice generates a series of qubits on a specific basis (e.g., horizontal, vertical, or diagonal polarization) and sends them to Bob over a quantum channel. Each qubit represents a bit of information that will eventually form the key.
2. Transmission and Measurement
Upon receiving the qubits, Bob measures them on a randomly chosen basis. Because of the superposition principle, if he chooses the same basis as Alice used to prepare the qubits, he will obtain the correct value. However, if he chooses a different basis, the outcome will be random.
3. Basis Reconciliation
After the transmission, Alice and Bob publicly share the bases they used for their measurements without revealing the actual measurement results. They discard the qubits where their bases did not match, keeping only the qubits measured on the same basis.
4. Key Generation
The remaining measurement results from the shared secret key. Before using this key for encryption, Alice and Bob can perform error correction and privacy amplification to ensure its security against potential eavesdropping.
Security Features of Quantum Cryptography
The security of quantum cryptography stems from its reliance on the principles of quantum mechanics. Here are some key security features:
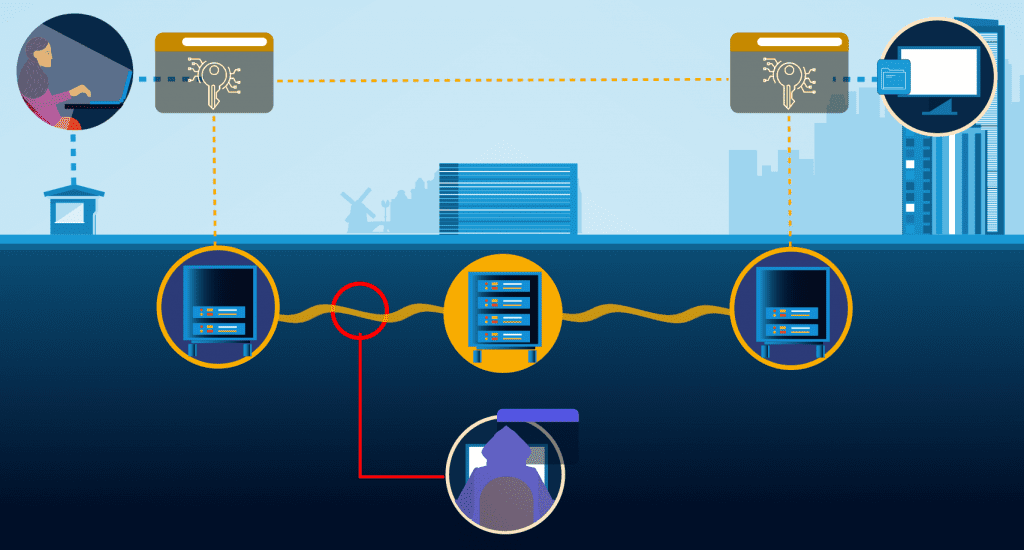
1. Eavesdropping Detection
In classical cryptography, eavesdropping can go undetected. However, in quantum cryptography, any attempt to intercept the communication will introduce detectable anomalies. If an eavesdropper, Eve, tries to measure the qubits, the act of measurement will disturb the quantum states, leading to errors that Alice and Bob can observe.
2. Unconditional Security
Quantum key distribution provides unconditional security, meaning that its security is not based on the computational hardness of mathematical problems, as is the case with classical cryptography. Instead, it relies on the laws of physics. Even with unlimited computational resources, an adversary cannot gain information about the key without being detected.
3. No-cloning Theorem
The no-cloning theorem states that it is impossible to create an identical copy of an arbitrary unknown quantum state. This principle ensures that an eavesdropper cannot simply duplicate the quantum states being transmitted, further enhancing security.
Practical Implementations of Quantum Cryptography
Quantum cryptography has advanced significantly since its inception in the 1980s. Various protocols and systems have been developed, with several key implementations:
1. BB84 Protocol
The BB84 protocol, proposed by Charles Bennett and Gilles Brassard in 1984, is the first and most widely studied QKD protocol. It uses the polarization states of photons to encode bits. The protocol has been implemented in various laboratory and commercial settings, proving its feasibility and security.
2. E91 Protocol
Developed by Artur Ekert in 1991, the E91 protocol relies on entangled photon pairs to achieve secure key distribution. The protocol leverages the concept of quantum entanglement to establish a shared key and detect eavesdropping.
3. Continuous Variable QKD
Continuous variable QKD protocols utilize properties of continuous quantum states, such as the quadratures of light fields. These protocols can be implemented using standard telecommunications technology, making them more practical for real-world applications.
4. Commercial Systems
Several companies and research institutions have developed commercial quantum cryptography systems. These systems are designed for secure communication over long distances and have been deployed in various sectors, including banking, government, and telecommunications.
Challenges and Limitations
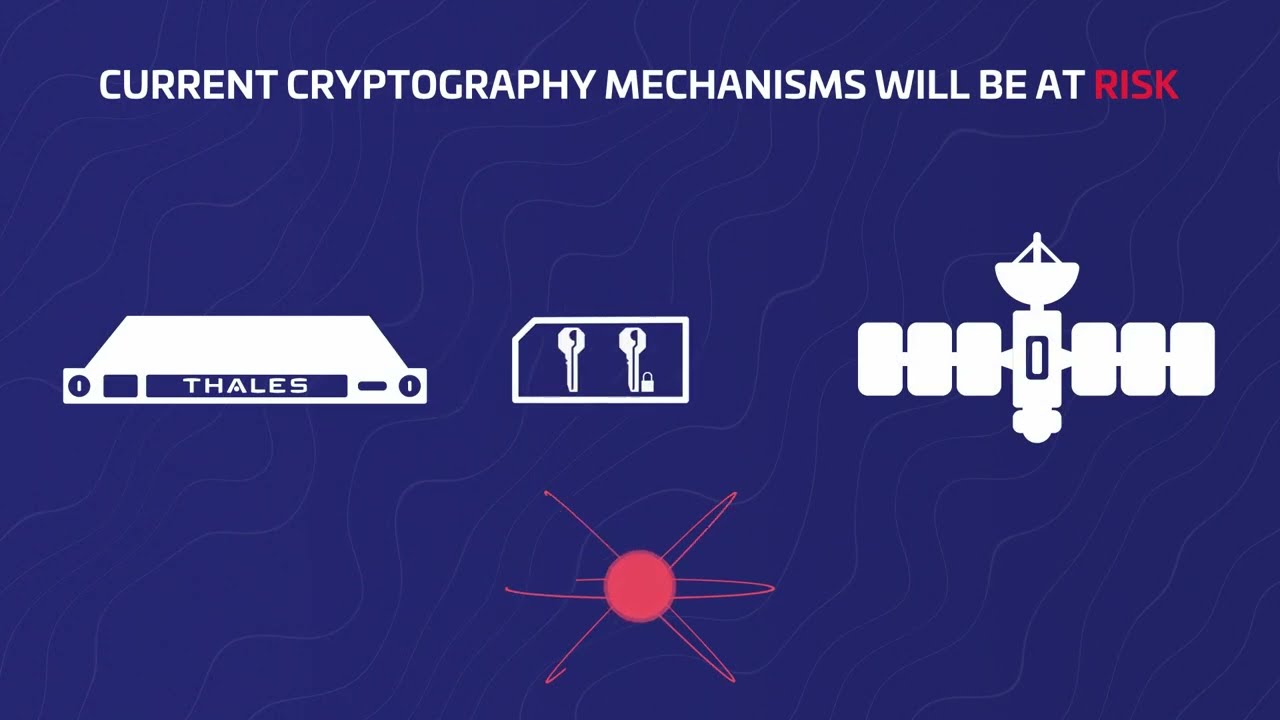
While quantum cryptography offers significant advantages, it also faces several challenges:
1. Distance Limitations
Quantum signals can degrade over long distances, leading to increased errors and potential security vulnerabilities. Current implementations of QKD are limited in range, typically around 100 to 200 kilometres without the use of repeaters.
2. Technological Challenges
Implementing quantum cryptography requires specialized hardware, such as single-photon sources and detectors, which can be expensive and complex to integrate into existing infrastructure. As technology advances, these challenges may be mitigated, but they currently pose barriers to widespread adoption.
3. Integration with Classical Systems
Quantum cryptography needs to be integrated with classical cryptographic systems for practical use. Developing hybrid systems that effectively combine both technologies presents technical and operational challenges.
4. Regulatory and Standardization Issues
The rapid development of quantum cryptography has outpaced regulatory frameworks and standardization efforts. Establishing universal standards for quantum cryptography will be essential for ensuring compatibility and security across different systems.
The Future of Quantum Cryptography
The future of quantum cryptography looks promising, with ongoing research and development efforts aimed at overcoming existing challenges. Key trends and advancements include:
1. Quantum Repeaters
Quantum repeaters are devices that could extend the range of quantum communication by enabling the entanglement of distant qubits. They hold the potential to make global quantum networks feasible, allowing secure communication over long distances.
2. Integration with Quantum Networks
Efforts are underway to create global quantum networks that can facilitate secure communication between multiple parties. These networks will leverage quantum key distribution and other quantum communication protocols to enhance security.
3. Advancements in Technology
Continued advancements in quantum technology, including improvements in photon detection, quantum memory, and error correction methods, will enhance the practicality and security of quantum cryptographic systems.
4. Research in New Protocols
Ongoing research is exploring new QKD protocols and approaches that could improve the efficiency, security, and scalability of quantum cryptography. This includes exploring new quantum systems and integrating classical cryptographic techniques.
Quantum cryptography represents a significant leap forward in secure communication, harnessing the principles of quantum mechanics to protect sensitive information. By offering unparalleled security features such as eavesdropping detection and unconditional security, quantum cryptography has the potential to revolutionize the way we secure data in an increasingly digital world. However, challenges related to distance limitations, technological complexities, and integration with classical systems must be addressed for widespread adoption.
As research and technological advancements continue, the future of quantum cryptography looks bright, promising a new era of secure communication. Embracing these innovations will be essential for safeguarding our digital lives against emerging threats and ensuring that the principles of quantum cryptography are effectively harnessed for the benefit of society.